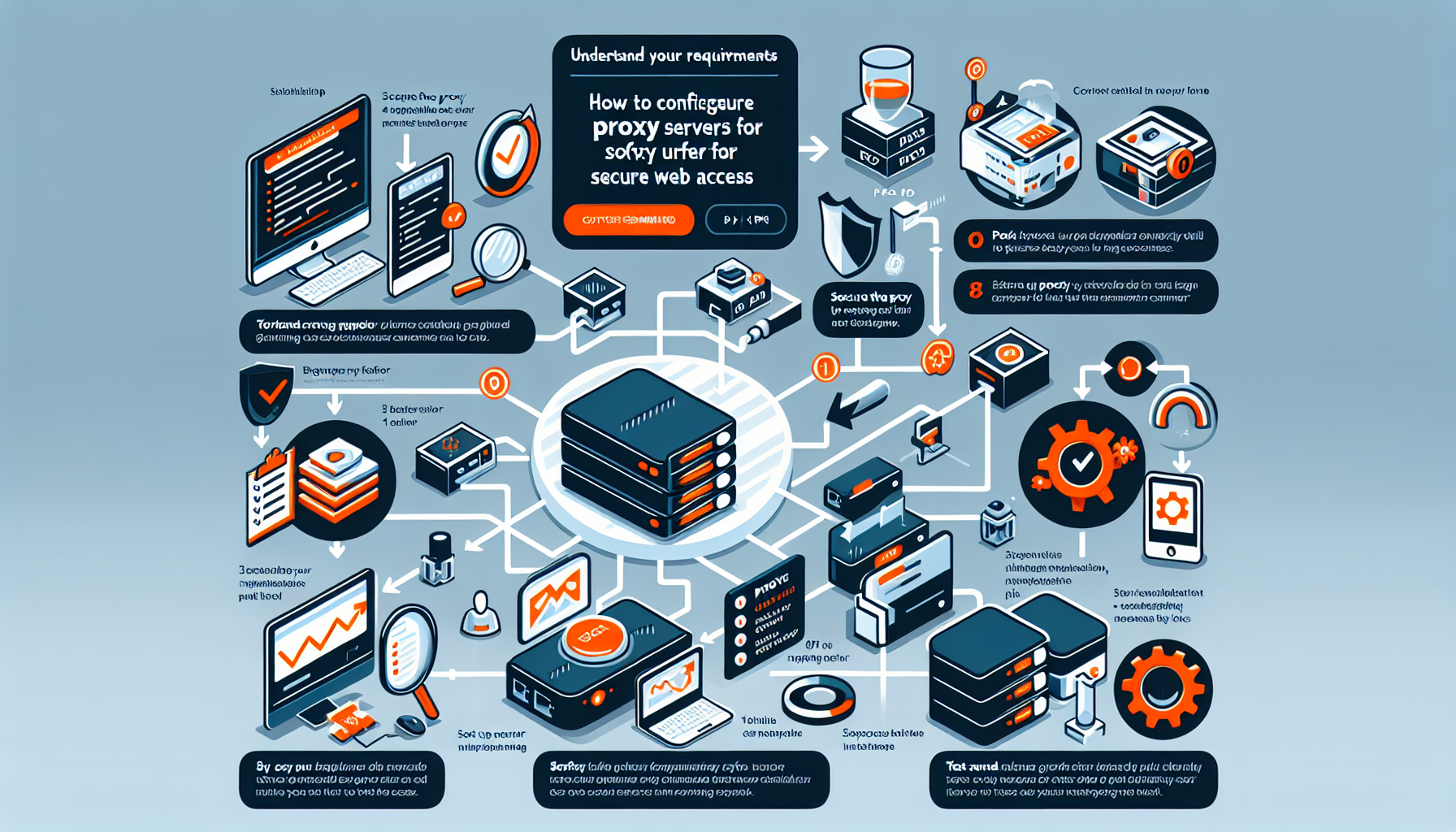
How do I configure proxy servers for secure web access?
Configuring proxy servers for secure web access involves several steps to ensure proper functionality and security. Here is a detailed guide tailored to an IT manager like yourself: 1. Understand Your Requirements Before configuring a proxy server: – Define the use case: Is it for web filtering, caching, anonymity, or improved security? – Determine the […]