How do I troubleshoot network connectivity issues?
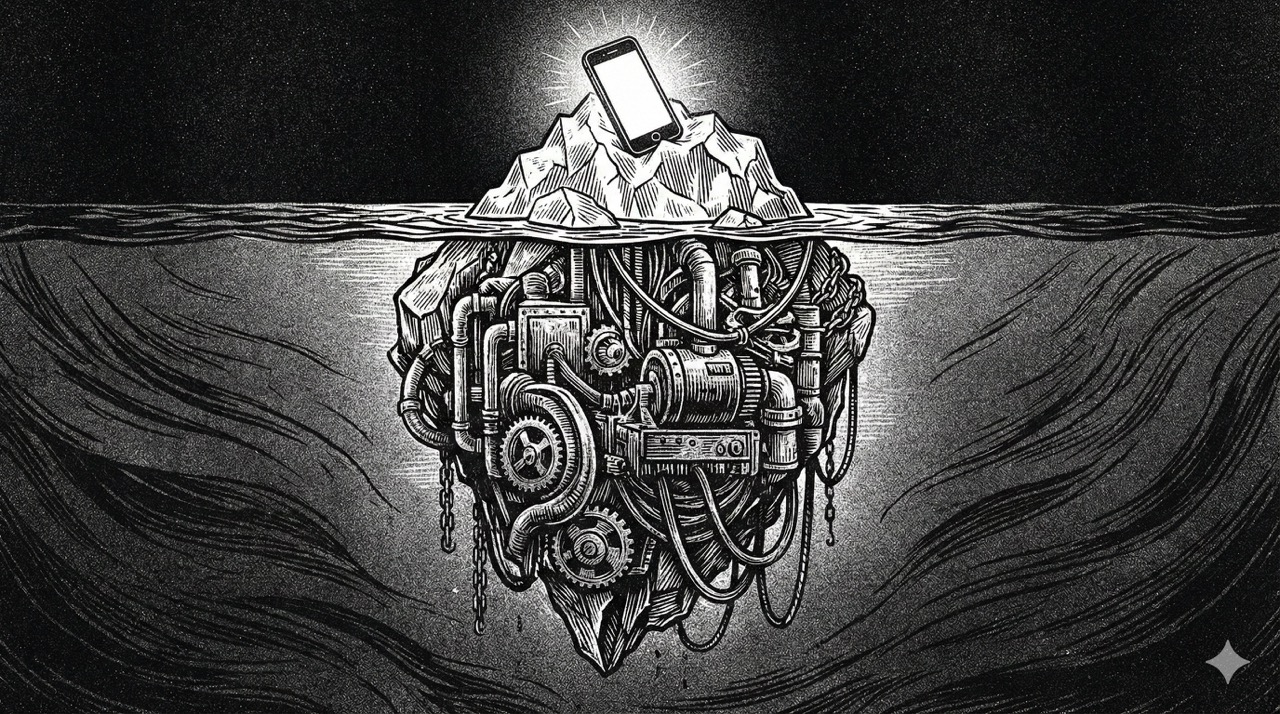
Troubleshooting Network Connectivity Issues: A Step-by-Step Guide from an Enterprise IT Perspective Network connectivity issues are a constant challenge in enterprise environments. In my experience managing large-scale datacenter networks and hybrid cloud infrastructures, the key to resolving these problems quickly lies in a structured approach—moving from physical layer checks to application-level diagnostics while leveraging the […]