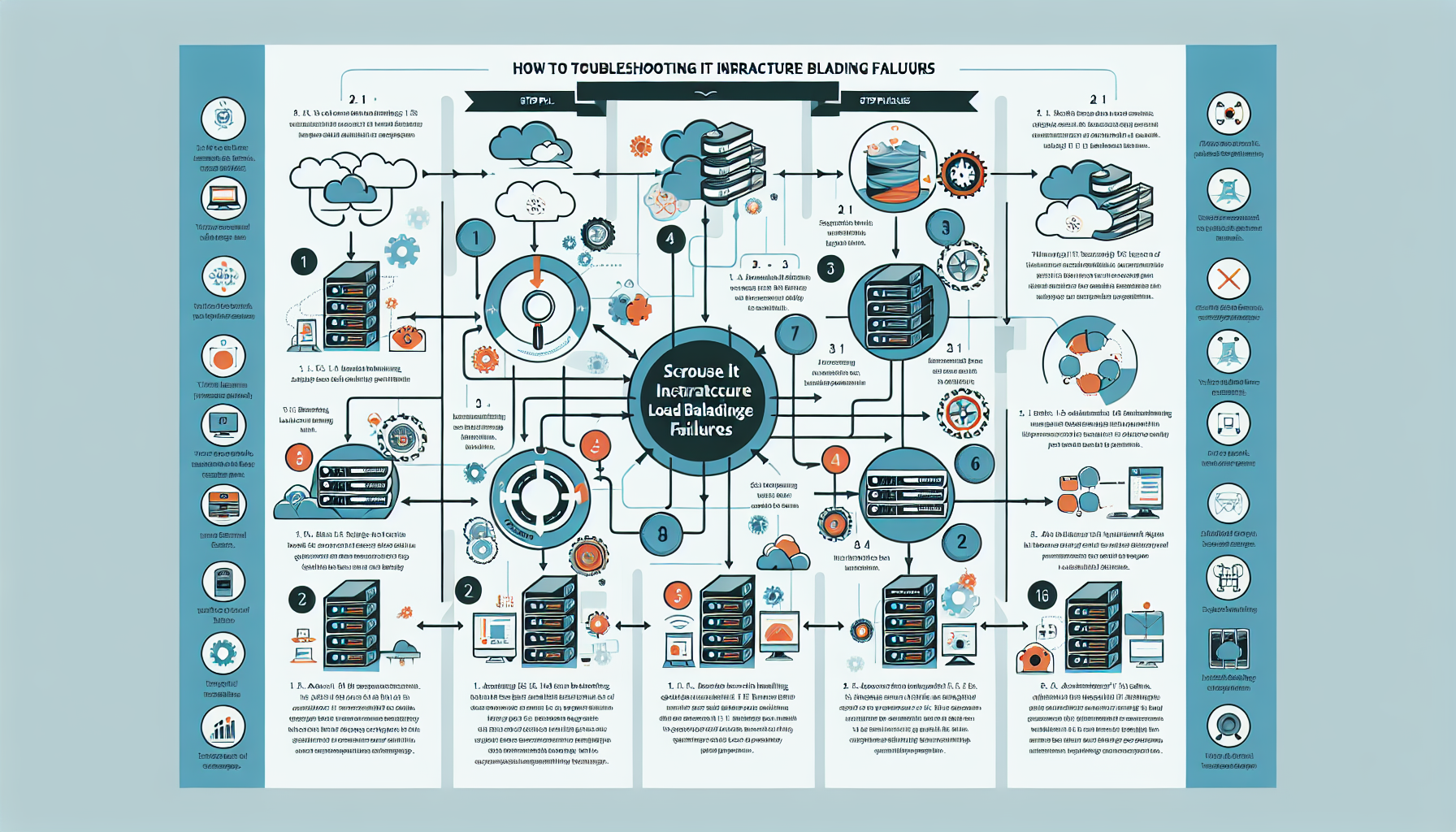
How do I troubleshoot IT infrastructure load balancing failures?
Troubleshooting load balancing failures in an IT infrastructure requires a structured, methodical approach to identify and resolve the issue effectively. Here’s a step-by-step guide you can follow: 1. Verify the Scope of the Problem Identify affected services and users: Determine if the issue is localized to a specific application, service, or user group or if […]