How do I secure IT infrastructure for research and development environments?
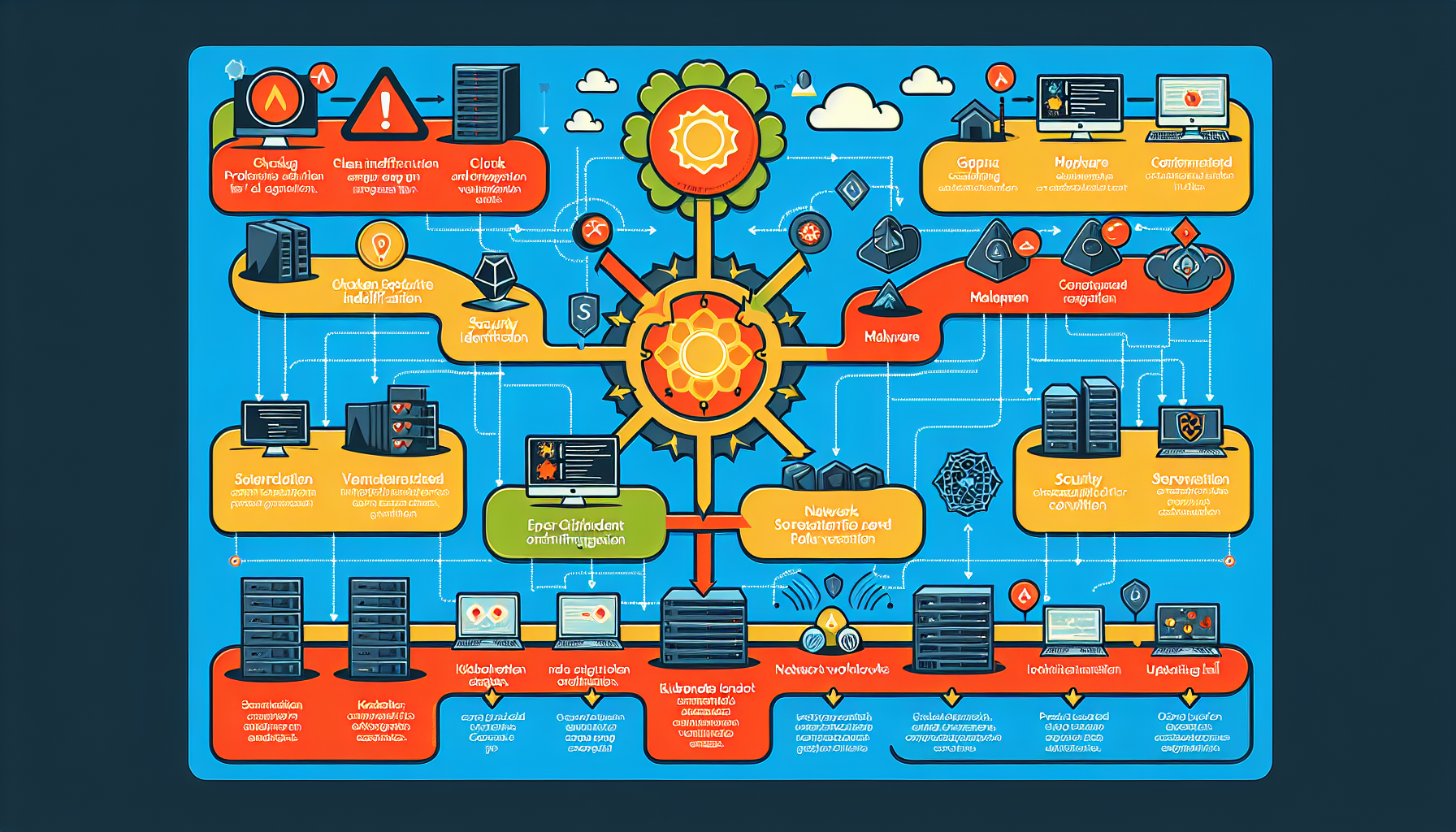
Securing an IT infrastructure for research and development (R&D) environments is critical, especially given the sensitive data, intellectual property, and experimentation that often takes place in such settings. Below are steps and best practices to ensure a robust security posture for R&D environments: 1. Understand the R&D Environment and Data Classify Data: Identify and categorize […]