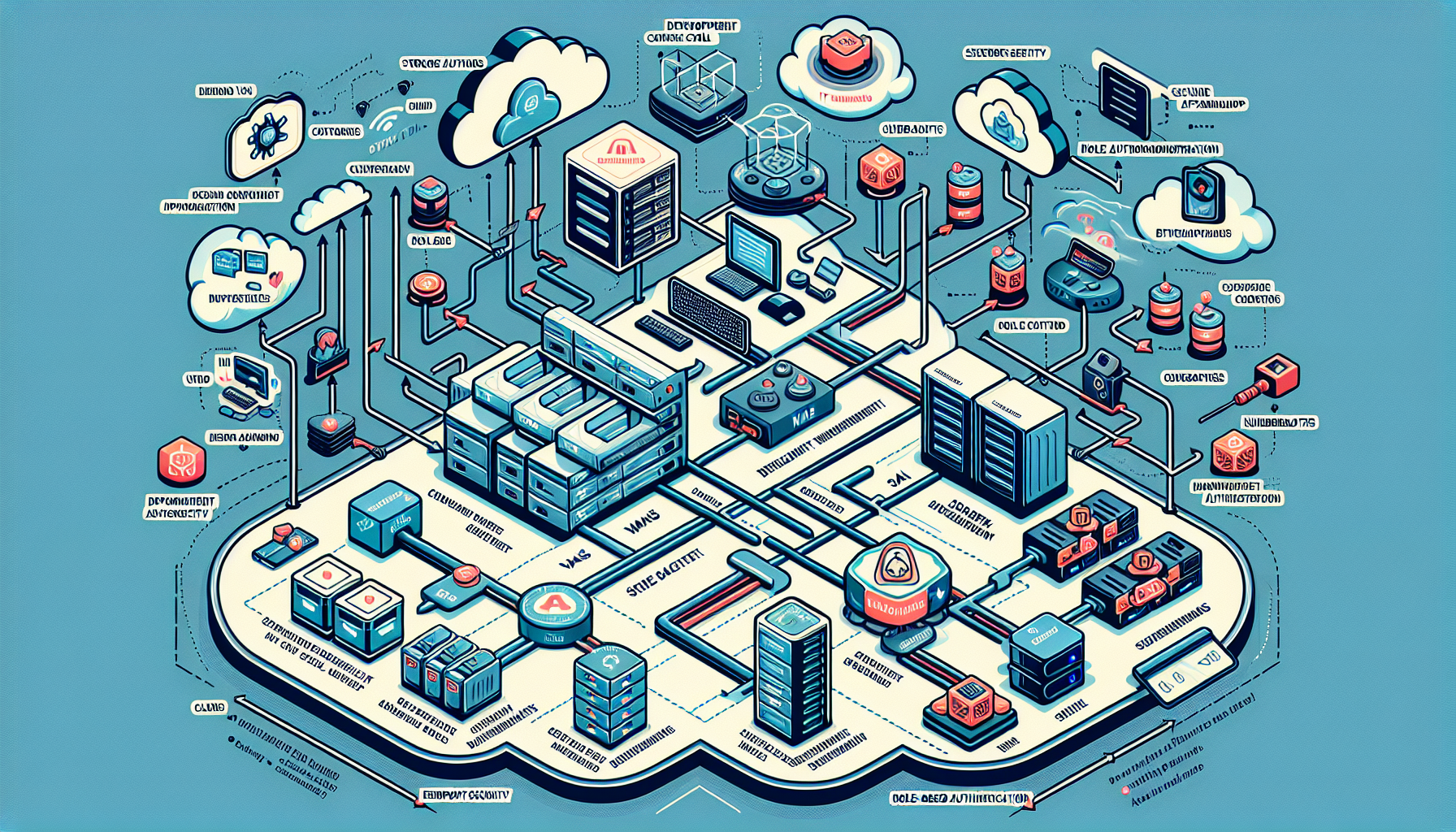
Configuring IT infrastructure for secure mobile application development requires a combination of best practices, security measures, and efficient resource management. Here’s a step-by-step approach tailored to your role and expertise:
1. Define Requirements and Assess Risks
- Understand Development Needs: Identify the programming languages, frameworks (e.g., Flutter, React Native), and tools used by developers.
- Risk Assessment: Assess security risks like unauthorized access, data leakage, and weak infrastructure configuration.
- Compliance: Ensure compliance with industry standards (e.g., GDPR, HIPAA, OWASP Mobile Security Project).
2. Design a Secure Development Environment
- Segregated Network: Create a segmented VLAN for development and testing environments. Prevent exposure to production systems.
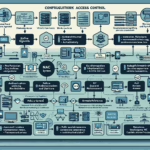
- Access Control:
- Use role-based access control (RBAC) to ensure developers and testers have minimal required access.
- Implement Multi-Factor Authentication (MFA) for all accounts.
- Secure Communication:
- Use VPNs or Zero Trust Network Access (ZTNA) for remote developers.
- Enforce TLS encryption for data in transit.
3. Virtualization and Containerization
- Virtualized Environment:
- Set up virtual machines (VMs) for development, QA, and staging environments using VMware, Hyper-V, or Proxmox.
- Leverage snapshots to quickly revert to a clean state.
- Containerization:
- Use Docker or Kubernetes for isolated environments that replicate production environments.
- Implement Kubernetes namespaces for logical separation of workloads.
4. Storage and Backup
- Centralized Storage: Deploy secure, scalable storage systems such as NAS or SAN to store source code and resources.
- Version Control: Use Git-based repositories (e.g., GitHub, GitLab, Bitbucket) with security features like branch protection and code scanning.
- Backup Strategy:
- Automate backups of repositories, databases, and storage.
- Store backups in a secure, offsite location and encrypt them.
5. Servers and Compute Resources
- Secure Servers:
- Harden operating systems (Linux/Windows) by disabling unnecessary services and ports.
- Install security patches regularly.
- GPU Servers for AI Integration:
- Deploy servers with NVIDIA GPUs if your mobile app requires AI/ML capabilities.
- Use frameworks like TensorFlow or PyTorch with containers for model training and inference.
- Scalability: Use cloud-based solutions (e.g., AWS EC2, Google Cloud Compute Engine) for dynamic resource allocation during development.
6. Implement Secure CI/CD Pipeline
- Continuous Integration:
- Use Jenkins, GitLab CI/CD, or Azure DevOps for automation.
- Integrate static code analysis tools (e.g., SonarQube) to detect vulnerabilities early.
- Continuous Deployment:
- Automate deployment processes with approval gates for production environments.
- Use container orchestration (e.g., Kubernetes) for automated rollouts and rollbacks.
7. Kubernetes for Mobile Backend
- Deploy backend services (e.g., APIs, databases) for the mobile app on Kubernetes clusters.
- Security Measures:
- Use Kubernetes RBAC for granular access control.
- Configure network policies to restrict service communication.
- Regularly update Kubernetes clusters and nodes.
- Monitoring:
- Implement monitoring tools like Prometheus and Grafana to track cluster performance.
- Use Kubernetes-native security tools like Falco for anomaly detection.
8. AI Integration
- Secure AI Workloads:
- Deploy AI models in isolated containers or on dedicated GPU nodes.
- Encrypt AI training datasets both at rest and in transit.
- Data Governance:
- Ensure proper labeling and anonymization of sensitive data used for AI/ML.
9. Endpoint Security
- Secure Developer Machines:
- Install endpoint protection tools (e.g., CrowdStrike, Bitdefender) on developer laptops and desktops.
- Enforce OS hardening policies and disable admin privileges.
- Mobile Device Security:
- Use Mobile Device Management (MDM) solutions to enforce security policies on test devices.
- Implement secure coding practices for mobile app development.
10. Regular Security Audits
- Vulnerability Scans:
- Conduct regular scans of infrastructure components using tools like Nessus or Qualys.
- Penetration Testing:
- Simulate attacks on the mobile app and backend systems to identify weaknesses.
- Code Reviews:
- Ensure developers follow secure coding practices and perform peer reviews.
11. Logging, Monitoring, and Incident Response
- Centralized Logging: Use tools like ELK Stack (Elasticsearch, Logstash, Kibana) or Splunk for centralized log management.
- Monitoring: Set up alerts for suspicious activities using tools like Datadog or Nagios.
- Incident Response Plan:
- Document and regularly test your response plan for security incidents.
- Train developers and IT staff on procedures during a breach.
12. Training and Awareness
- Conduct regular security training for developers on secure coding practices and tools.
- Share industry security trends and updates (e.g., OWASP Mobile Top 10 vulnerabilities) with the team.
13. Cloud Considerations
- Cloud Security:
- Use Identity and Access Management (IAM) in AWS, Azure, or Google Cloud to restrict access.
- Enable encryption for storage buckets and databases.
- Cost Optimization:
- Use reserved instances or autoscaling to save costs while maintaining performance.
By implementing these steps, you can ensure a robust, secure, and scalable IT infrastructure tailored for mobile application development.
How do I configure IT infrastructure for secure mobile application development?