What are the best practices for securing IT infrastructure logs?
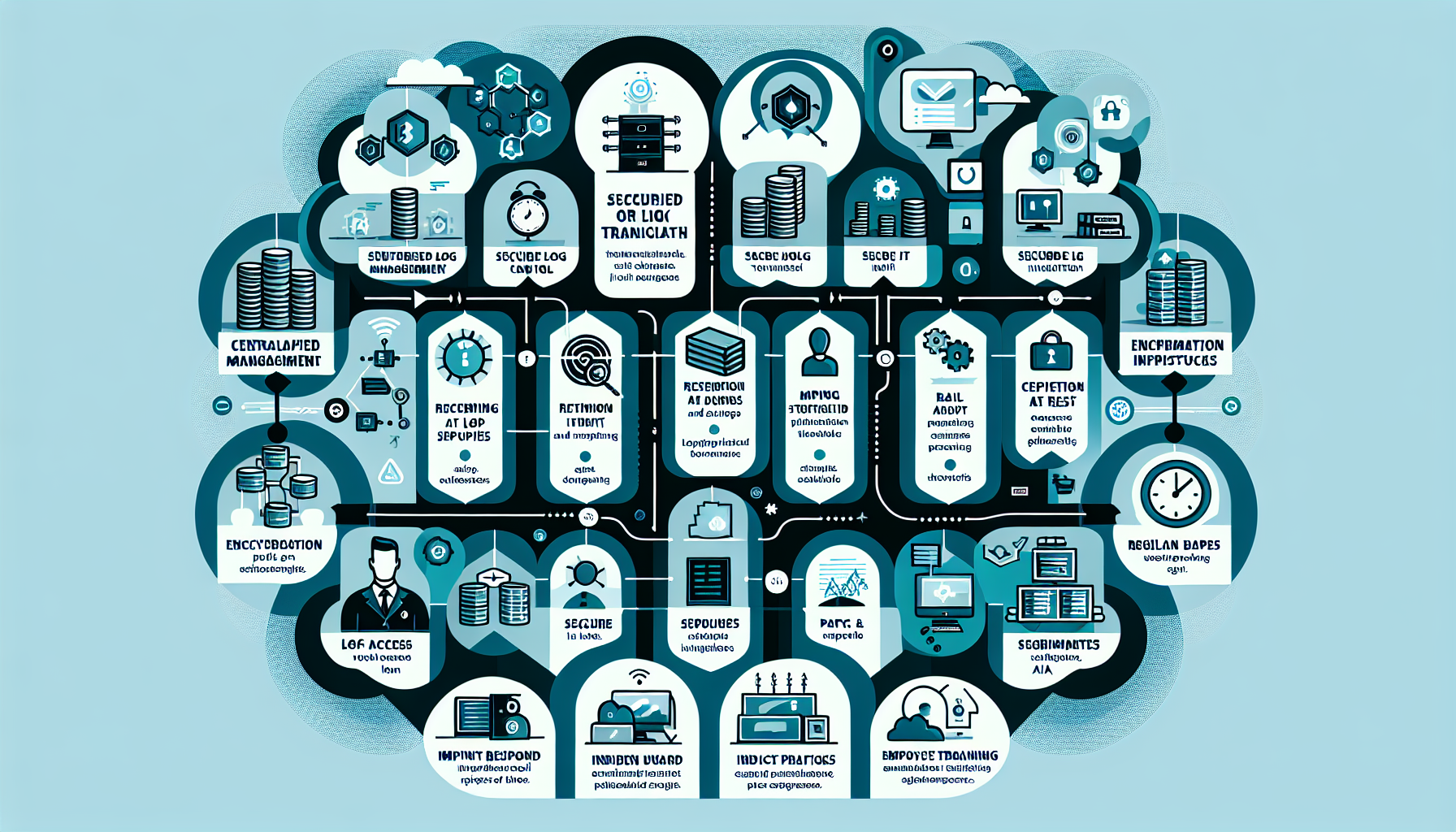
Securing IT infrastructure logs is a critical aspect of maintaining a robust and resilient IT environment. Logs contain valuable information that can help diagnose issues, monitor performance, and detect security threats. However, if not properly secured, they can become a target for attackers. Below are the best practices for securing IT infrastructure logs: 1. Centralized […]